Next-Generation Firewall
UserGate Next-Generation Firewall (NGFW) offers a high level of protection from threats for networks of any size and architecture by providing maximum visibility for security events.
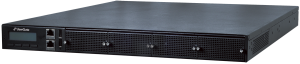
The different supply options such as a hardware and software system (HSC), a virtual appliance and SECaaS (Security as a Service), open up an infinite variety of scenarios for integrating UserGate security features into your IТ architecture.
Online Demo
Maximum Visibility
A key aspect of strong network security is providing visibility for security events, which include all kinds of user, application, and device activity. Therefore, the ability to see, analyze, and interpret all this activity plays a huge role in creating a secure IT infrastructure. This is impossible to achieve without high-quality and high-performance SSL traffic inspection. Thanks to our advanced technology, UserGate Next-Generation Firewall (NGFW) can decrypt all traffic, including TLS 1.3.
How UserGate Next-Generation Firewall (NGFW) Works
- Messengers
- VPN clients
- Remote access applications
- Torrent clients
A regular firewall can only see IPs and ports. However, the same port can be used by numerous applications. With UserGate Next-Generation Firewall (NGFW), you can see all the applications.
Benefits of UserGate Next-Generation Firewall (NGFW)
Maximum Visibility for Security Events
Detect hidden attacks on your IT infrastructure and respond to them in a timely manner
Powerful Security Features
Increase your network security arsenal with the built-in and add-on security features
Flexible Supply Options
NGFW can be supplied as a hardware and software system (HSC), as a virtual firewall appliance, or on a Security-as-a-Service (SECaaS) basis
Multiple Modes of Operation
Select the desired mode of operation and feature set for your UserGate Next-Generation Firewall (NGFW) device
Integration Options
The different integration options allow you to select a format that suits your IT infrastructure best
Part of Ecosystem
UserGate Next-Generation Firewall (NGFW) is a part of the UserGate SUMMA security product ecosystem
Applications of UserGate Next-Generation Firewall (NGFW)
Security Web Gateway (SWG)
Powered by the proprietary rProxy engine, the technologies and features within UserGate Next-Generation Firewall (NGFW) allow for using it as a gateway for secure Internet access. The user authorization, application identification, and traffic decryption technologies employed ensure maximum visibility for network security events and assist in the fine-tuning of security policies and provision of deep analytics.
Intrusion Detection & Prevention System (IDPS)
The intrusion detection and prevention system based on a proprietary engine quickly analyzes network connections to check for malware. Together with the expertise from the Monitoring and Response Center, IDPS becomes a full-fledged intrusion protection solution.
Zero Trust Network Access (ZTNA)
The user authorization, application identification, and network traffic decryption technologies employed in UserGate Next-Generation Firewall (NGFW) place it at the core of the Zero Trust Network Access security concept.